Latest blog articles
-
I am very pleased that today we will start teaching the EU and Global Cybersecurity Fundamentals course within the Advanced Master in Privacy, Cybersecurity and Data Management LLM we created at ECPC. Today we will kick off the course with Brian Honan, who will lecture on the concept of...
-
When we think of cybersecurity we are generally concerned with the code, algorithms and systems that are responsible for the functioning of out digital technologies and the safety of our sensitive data. What has become increasingly apparent is the role of humans in ensuring the security of our...
-
Since “Champagne” is a protected designation of origin (PDO) under EU law, it is not self-evident whether a product that is not Champagne but which contains Champagne can use the protected term in its trade name.
-
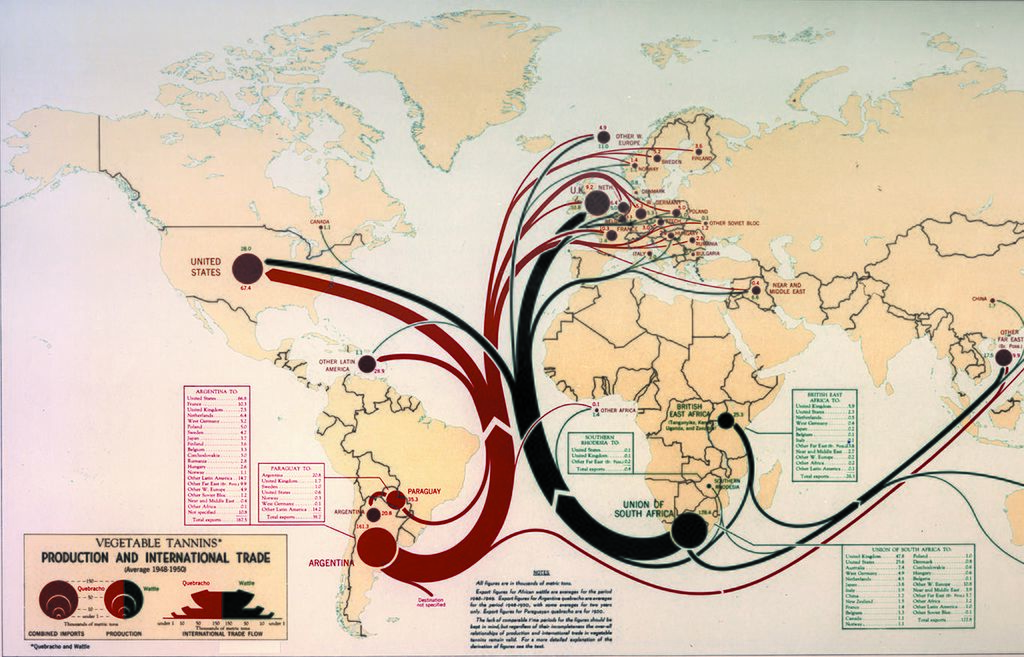
This book addresses concerns with the international trade and investment dispute settlement systems from a statist perspective, at a time when multilateralism is deeply questioned by the forces of mega-regionalism and political and economic contestation.
-
Published on MLR blogs. What do documents about negotiations of the Transatlantic Trade and Investment Partnership (TTIP), oversight of the EU’s Food Safety Authority or Tax-Justice have in common? In order to access these documents, (selected) Members of the European Parliament are requested to...
-
On Tuesday, the Grand Chamber of the Court of Justice of the European Union declared the Commission’s US Safe Harbour Decision invalid. The Court’s ruling in Case C-362/14 of the Austrian Internet activist Maximillian Schrems v the Irish Data Protection Commissioner is a milestone in the...
-
The EU is negotiating trade agreements in secret because orthodoxy, mysticism and a wishful thinking-based approach to policymaking have returned to power in Europe.