Latest blog articles
-
Today it has become impossible for one single person to master the whole field of environmental law, given its complexity and dynamic developments. Indeed, with the increasing manifestation of environmental crisis, law, being a powerful tool to address polluting behaviour, has become utterly complex...
-
I am very pleased that today we will start teaching the EU and Global Cybersecurity Fundamentals course within the Advanced Master in Privacy, Cybersecurity and Data Management LLM we created at ECPC. Today we will kick off the course with Brian Honan, who will lecture on the concept of...
-
Achieving a sustainable way of life requires massive societal changes and (private international) law should enable, rather than hamper, the realization of such essential goals.
-
This blog post is a re-elaboration of my interview this morning with Luca Bertuzzi, Digital & Media Editor from EurActiv, available here.
-
“The SolarWinds Attack is, to date, the most visible, widespread, and intrusive information technology (‘IT’) software supply chain attack – i.e., a cyber attack that corrupts IT software and uses that software as an attack vector. Supply chain attacks are dangerous because the malware is embedded...
-
Over the last 20 years, access to cheap computational capacity has increasingly led to the harvesting of more and more personal data, without having to worry too much about costs related to data storage and processing activities.
-
What was promised by the GDPR (Art. 80 and Rec. 142) is now a reality!
-
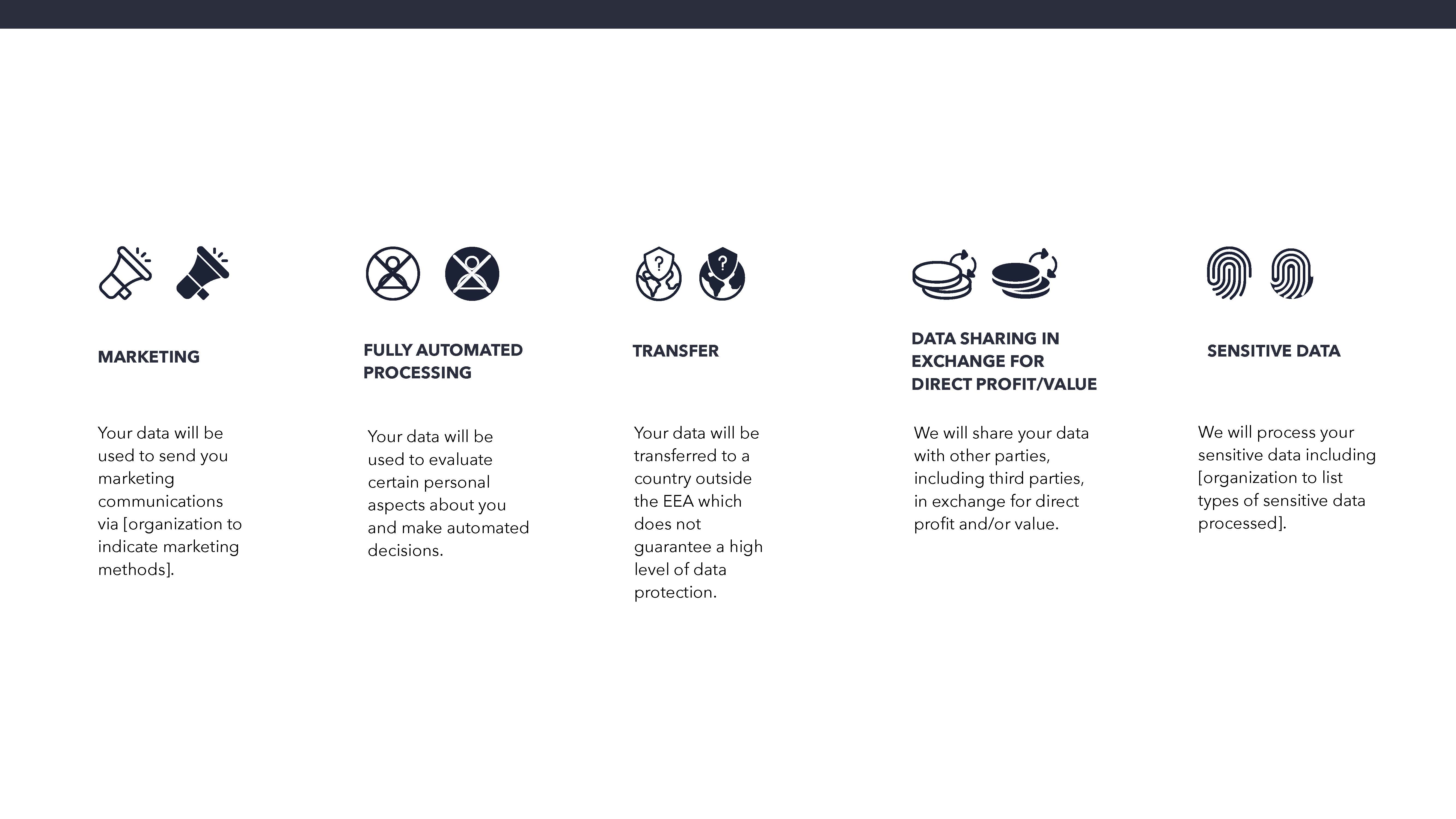
Survey on the Maastricht University Data Protection as a Corporate Social Responsibility (UM DPCSR) Icons Version 1.0 to facilitate users’ understanding of how their data is used.
-
Could you estimate how much time of your day you spend on social media? The answer would most likely be something along the lines of ‘a lot’ or ‘I’m always connected, so I get notifications all the time anyways’ but an actual estimate, that’s a very tough guess to take. However, for most people, it...
-
One view on social media communication is that platforms should remove content deemed to be inappropriate or disturbing and suspend users who have repeatedly violated the Community Guidelines and should do so in a consistent and coherent manner. A contrasting view is that users can share what they...